The latest Sophos annual study of the real-world ransomware experiences of manufacturing and production organizations explores the full victim journey, from attack rate and root cause to operational impact and business outcomes.
This year’s report incorporates new areas of study for the sector, including an exploration of ransom demands vs. ransom payments. Plus, for the first time, it shines a light on the role of law enforcement in ransomware remediation.
Download the report from the Sophos Partner Portal to get the full findings.
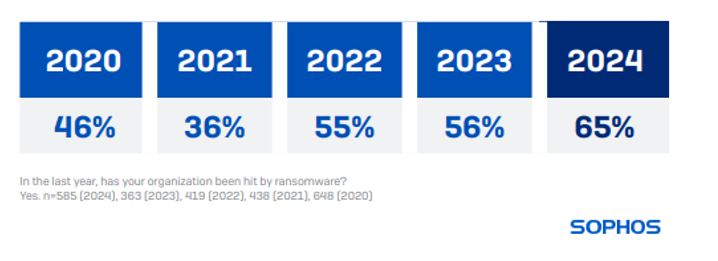
Attack rates and recovery costs have both gone up
65% of manufacturing and production organizations reported they were hit by ransomware last year. This is a notable increase from the previous two years (56% in 2023 and 55% in 2022) and represents a 41% increase since 2020.
93% of manufacturing organizations hit by ransomware in the past year said that the cybercriminals attempted to compromise their backups during the attack. Of them, 53% of backup compromise attempts were successful.
Additionally, three out of four ransomware attacks on manufacturing organizations (74%) resulted in data encryption, the highest encryption rate for the sector in the last five years. This rate is also higher than the 2024 cross-sector average of 70%.
In 2024, manufacturing organizations reported a mean cost of $1.67M to recover from a ransomware attack, an increase from the $1.08M reported in 2023.
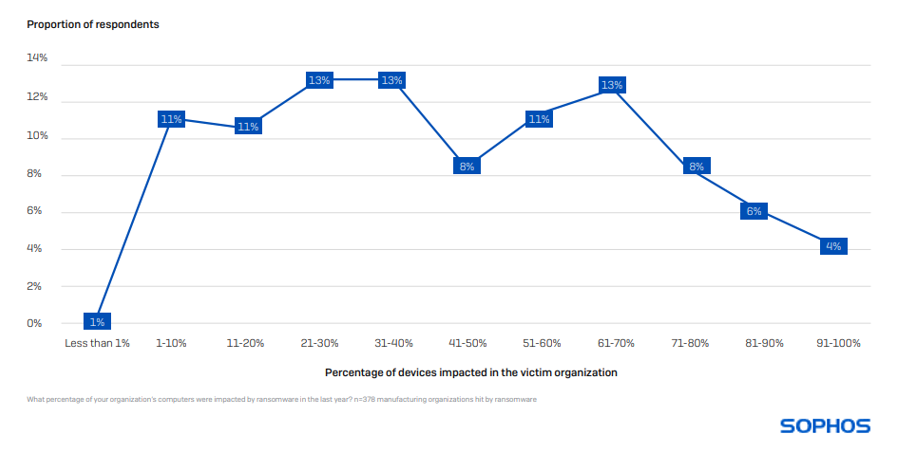
Devices impacted in a ransomware attack
On average, 44% of computers in manufacturing and production are impacted by a ransomware attack. Having your full environment encrypted is extremely rare, with only 4% of organizations reporting that 91% or more of their devices were impacted.
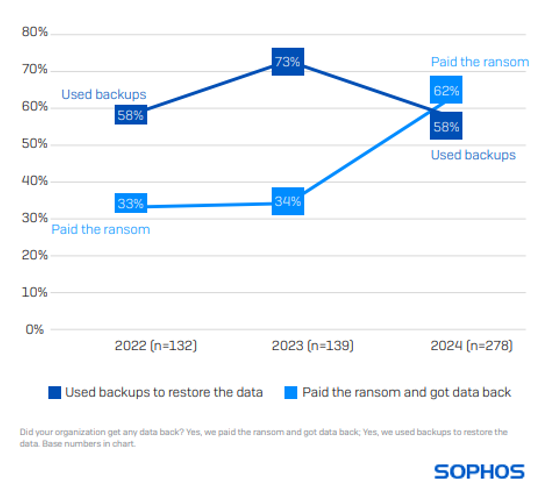
Six in ten victims now pay the ransom
While 58% in manufacturing restored encrypted data using backups, 62% paid the ransom to get data back. The percentage of manufacturing organizations that paid the ransom has almost doubled from our 2023 study when the sector reported one of the lowest ransom payment rates (34%) across all sectors.
A notable change over the last year is the increase in the propensity for victims to use multiple approaches to recover encrypted data (e.g., paying the ransom and using backups). This time around, almost half of manufacturing organizations (45%) that had data encrypted reported using more than one method, more than double the rate reported in 2023 (19%).
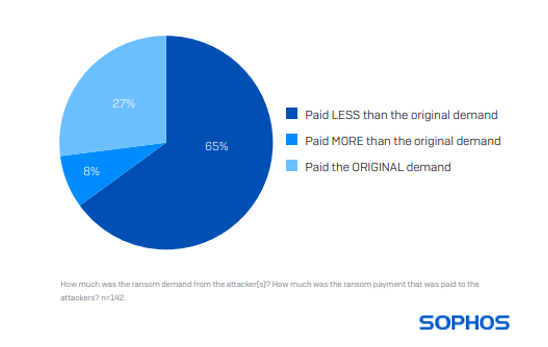
Ransom payments have soared – but victims rarely pay the sum demanded
157 manufacturing respondents whose organizations paid the ransom shared the actual sum paid, revealing that the average (median) payment has increased by 167% over the last year, from $450,000 to $1.2M.
While the ransom payment has increased, only 27% of manufacturing victims said that their payment matched the original request. 65% paid less than the original demand, while only 8% paid more.
Download the full report from the Sophos Partner Portal for more insights into ransom payments and many other areas.
Generate demand for your business
Make the most of Sophos partner marketing resources to run a successful partner marketing campaign to educate your audiences and generate demand for your business. The ready-to-run campaign kit includes the pdf report, a complete PowerPoint deck, and co-brandable email templates.
Access partner marketing campaign assets
About the survey
The report is based on the findings of an independent, vendor-agnostic survey commissioned by Sophos of 5,000 IT/cybersecurity leaders across 14 countries in the Americas, EMEA, and Asia Pacific, including 585 from the manufacturing and production sector. All respondents represent organizations with between 100 and 5,000 employees. The survey was conducted by research specialist Vanson Bourne between January and February 2024, and participants were asked to respond based on their experiences over the previous year.