Please be sure to share these recommendations with your Sophos Firewall customers or implement them yourself if managing your customer firewalls.
1. Update The Firmware with Every Release
If you only take away one thing from this article, it’s this. And this recommendation doesn’t just apply to firewalls, but all networking infrastructure. Most Sophos Firewall OS firmware updates include important security fixes. The best way to harden the firewall is to ensure it’s running the latest firmware. For Sophos Firewall, we just released v19.5 MR1 which includes a number of great new features, a significant performance boost, and several fixes.
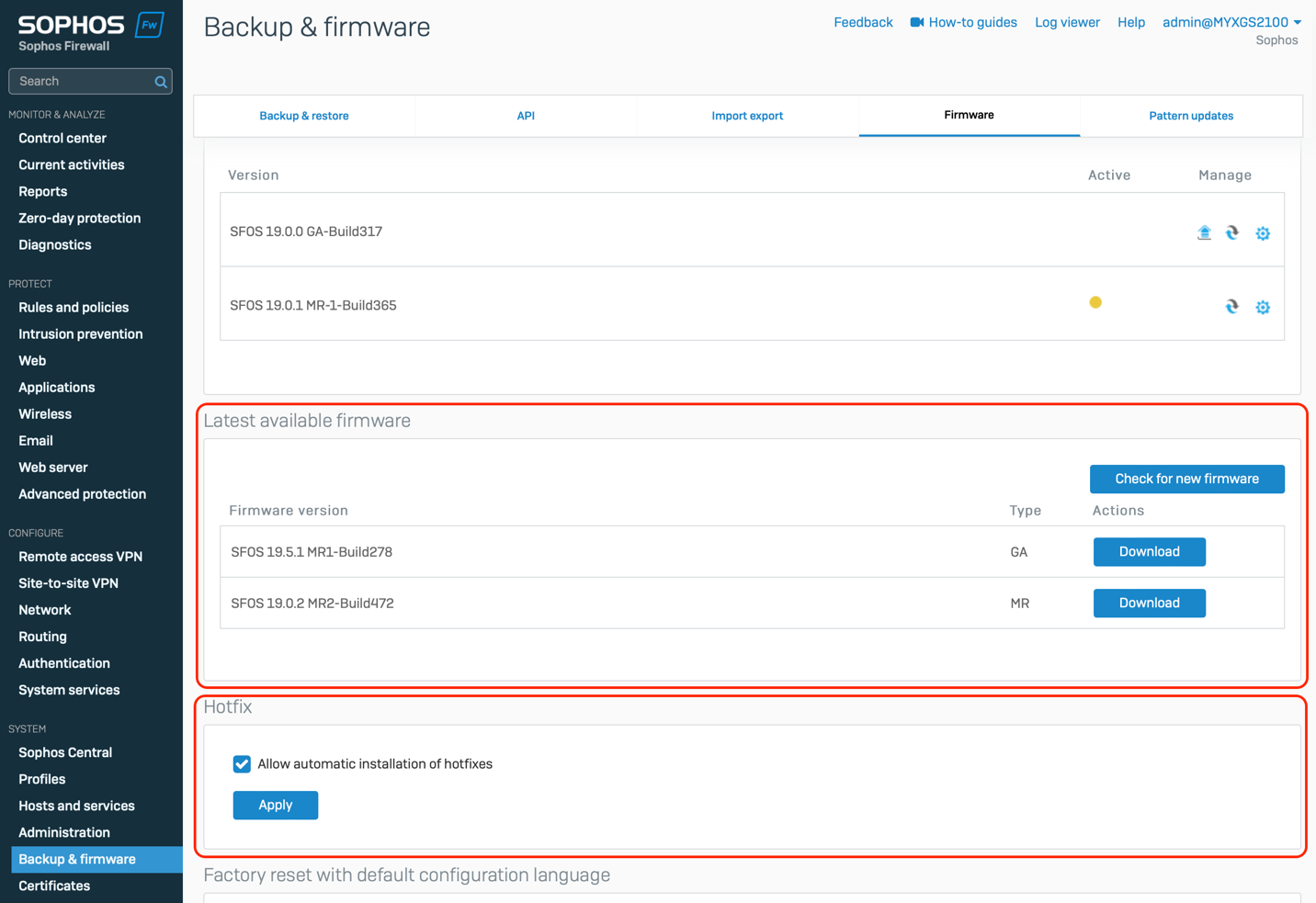
You can always find the latest firmware release on the firewall device by simply navigating to Backup and Firmware > Firmware (as shown below).
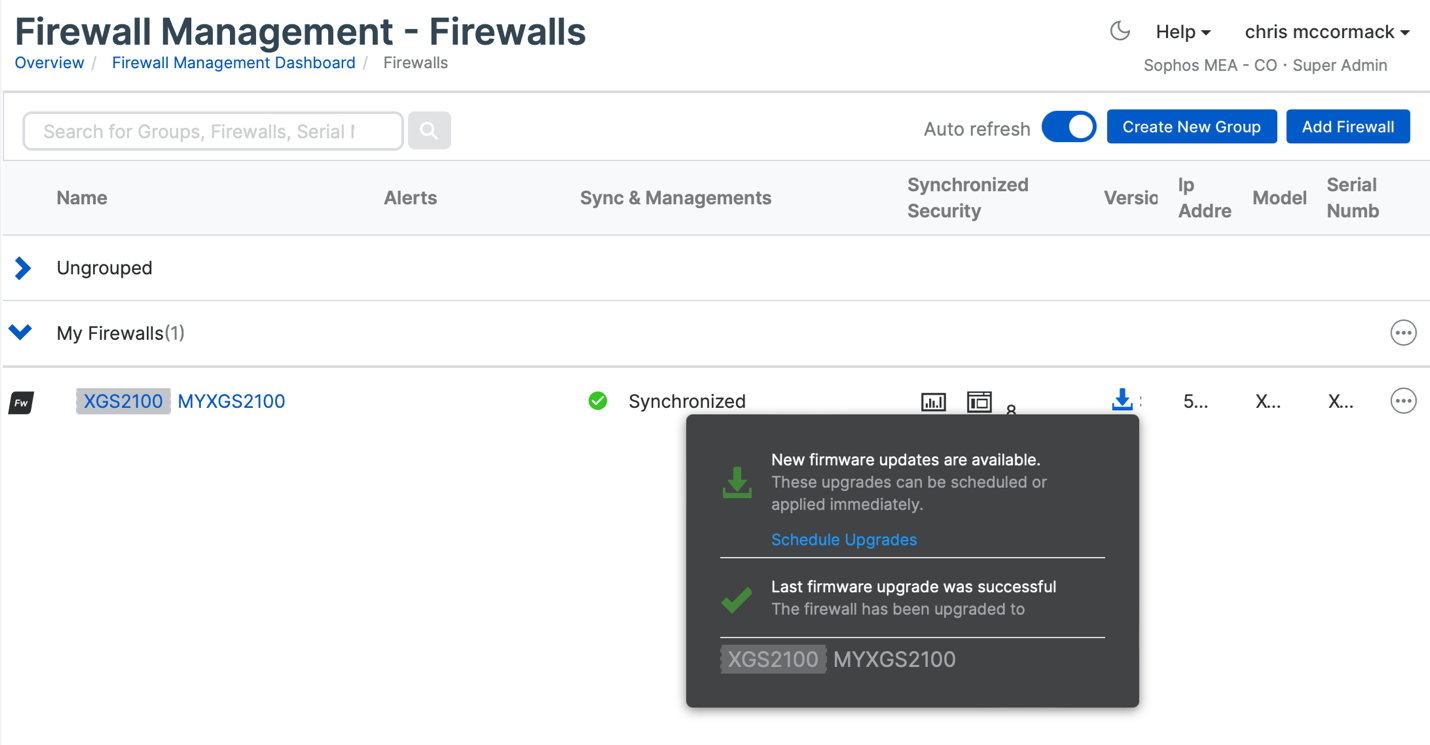
In Sophos Central, simply click the download arrow for the firewall you want to upgrade and choose “Schedule Upgrades”.
2. Enable Hotfixes
Occasionally, patches for vulnerabilities and other security fixes are released between regular firmware updates. This is done by applying hotfixes to the firewall automatically so its vitally important that this feature be enabled on all firewalls. While it’s enabled by default, some customers and partners have disabled this. If you are one of those, it’s highly recommended you go back and turn this feature on. This feature is found by navigating to Backup and Firmware > Firmware – check that “Allow automatic installation of hotfixes” is enabled (as highlighted at the bottom of the first screen shot above).
3. Limit Access to Firewall Services
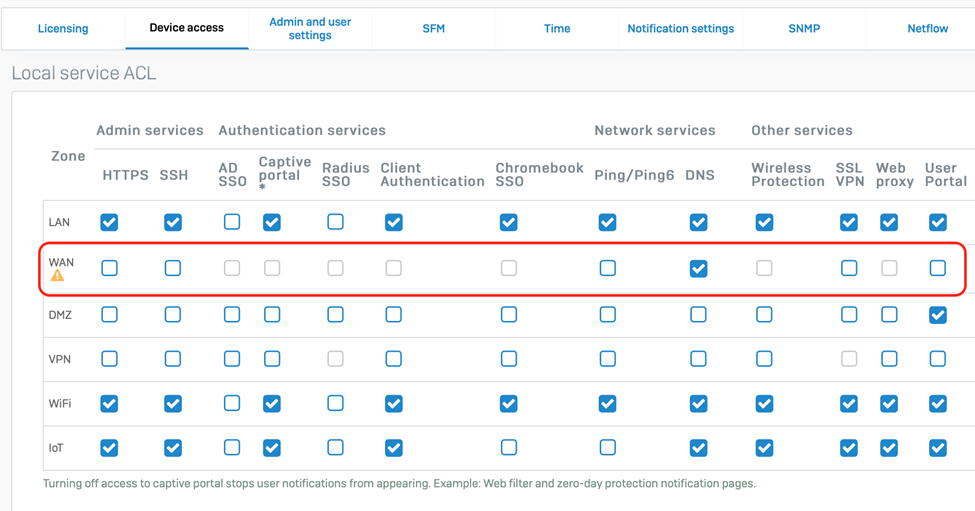
Sophos Firewall offers a number of ways to limit access to services that are not required to reduce exposure on the WAN. You should periodically check the device access settings and ensure that all unnecessary services are disabled (unchecked) on the WAN (see screen shot below). In particular, it’s strongly recommended that you disable remote admin via HTTPS and SSH, as well as the Captive Portal and User Portal on the WAN. Use Sophos Central, VPN or ZTNA to manage firewalls remotely. See the product documentation for instructions on how to manage device access.
4. Utilize Multi-Factor Authentication and Role-Based Administration
Enable multi-factor authentication (MFA) or one-time-passwords (OTP) and enforce strong passwords to protect the firewall from unauthorized access from stolen credentials or brute force hacking attempts. Sophos Firewall supports a rich set of MFA authentication options including new Azure AD single-sign-on authentication for webadmin access which can be super convenient (video / documentation).
Also consider taking advantage of Sophos Firewall’s granular role-based administration profiles to limit limit access for administrators of the firewall. Provide read-only access to administrators that don’t absolutely need control over various firewall functions.
5. Additional Best Practices for Securing Your Network from Ransomware
While you’re looking at ways to better secure your customer’s networks, I suggest you take a look at our recommended best-practices for securing the broader network from the latest ransomware and other advanced threats. With Sophos Firewall, your customers are already well on their way to better protecting their network, but there may be other Sophos solutions they are overlooking that can further help secure their organization.
Download the Guide from the Sophos Partner Portal to get the full set of best practices, plus promotional materials to share this handy guide with your customers.